How to deal with the threat to confidential information security posed by the rapid growth of the number of WIFI devices?
With the rapid popularization of Internet of Things (IoT) devices, the number of WiFi devices in home and enterprise networks is rapidly expanding. While these smart devices improve the convenience of life, they also multiply network security risks. The ubiquitous connection of WiFi devices has expanded the potential network attack surface, and information security is facing unprecedented challenges. How to deal with the threat to information security posed by the rapid growth of the number of WIFI devices has become the focus of attention of relevant departments. Mobile phones, as the most widely used WIFI devices, have become a convenient and fast way to transmit and obtain information. In particular, the functions of mobile phones are becoming more and more powerful. Improper use of mobile phones has become a new means of criminal leakage, especially in some special occasions, such as schools, conference rooms, military camps, etc., where electronic equipment needs to be shielded. Improper use of mobile phones poses a threat to confidential information security.
At present, there are more and more leaks caused by wireless eavesdropping, ranging from threatening personal privacy to endangering national security. Wireless eavesdropping refers to the transmission of stolen information in the form of electromagnetic emission. It is a general term for wireless eavesdropping, stealing photos, stealing videos, and stealing recordings. Wireless eavesdroppers are developing in the direction of miniaturization, intelligence, and encrypted transmission. The difficulty of detection is increasing, posing a serious threat to the security of state secrets and citizens' personal information security. To prevent wireless eavesdropping, the most important thing is to find hidden eavesdroppers. Wireless signal detectors are specially designed for special application scenarios such as schools, conference rooms, and military camps. They can find suspicious signal sources by analyzing wireless signals of different frequency bands such as WIFI, hotspots, and Bluetooth, and detect and locate them.
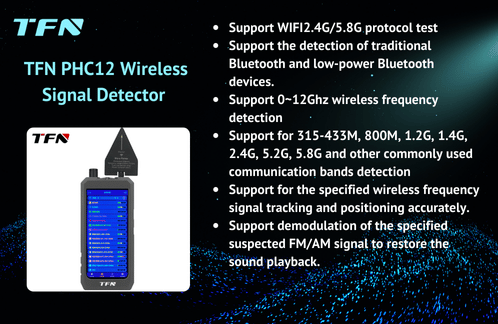
TFN PHC12 wireless signal detector (wireless signal activity analyzer) has the ability to detect wireless signals in all directions and good electromagnetic compatibility; high sensitivity, adjustable threshold, and large detection frequency range; small size, easy to carry, and deeply recognized by departments with information confidentiality. PHC12 has the following functions:
1. Support WIFI, covering all channels
2. Can distinguish WIFI hotspots, connected devices, unconnected devices and camera devices
3. Support detection of traditional Bluetooth and low-power Bluetooth devices and precise positioning of specified Bluetooth signals
4. Support 0-12GHz wireless spectrum monitoring, covering most wireless signal bands in the world
5. Support detection of commonly used communication frequency bands and precise positioning of specified wireless frequency models
6. Support alarms for wireless communication electronic devices that steal secrets in commonly used communication frequency bands
7. Support demodulation and restoration of sound playback of specified suspected FM/AM signals
8. Support precise tracking and positioning of specified WIFI access points or terminals
9. Support external multi-type antennas to enhance more accurate detection and analysis of specified signals
10. Scanning cycle of <500ms to ensure real-time capture of all wireless signals
In addition to wireless signal detectors, TFN also has more professional wireless signal/terminal detection and analysis equipment, such as: full-band signal search equipment in fixed environments, mobile phone plain text translation equipment, WIFI transmission protocol detection equipment, hidden camera scanning equipment, mobile phone content compliance inspection equipment, etc., to ensure information security in special departments and special application scenarios.
At the personal level, everyone needs to have the awareness of protecting personal information security. Faced with the rapid growth of the number of WiFi devices, we should not only enjoy the convenience brought by smart life, but also ignore the importance of information security. By strengthening password policies, enabling advanced encryption, network isolation, regular updates, device management, disabling unnecessary functions, user education, multi-factor authentication, security software configuration, and regular backups and emergency plans, we can effectively respond to the increasing security threats and build a solid line of defense for the information security of families and enterprises.
Strengthen password policies: Use uppercase and lowercase letters, numbers and special characters in passwords, and change them regularly. Avoid using default passwords, especially those that are easy to guess, to reduce the possibility of being attacked.
Enable advanced encryption: It is currently recommended to use the WPA3 encryption protocol, which can provide more advanced security features and stronger protection.
Network isolation: Reasonably isolate the home or enterprise network and protect core data and devices by dividing different subnets.
Regular updates: Regularly check and update the firmware and software of routers, WiFi connection devices and other network hardware to ensure that the system is always in the most secure state. For devices that no longer provide update support, consider replacing them with new devices with higher security as soon as possible.
Device management: Assign a unique identity and permissions to each device to ensure that each device can only access its necessary resources.
Disable unnecessary functions: Disable unused functions and services, such as remote management functions, to reduce the attack surface. Close unnecessary open ports to eliminate the opportunity for hackers to scan and exploit ports.
User education: Regularly carry out information security training to popularize knowledge such as password management, social engineering attack prevention, and phishing identification. Cultivate users' good Internet habits to prevent security risks caused by personal behavior.
Multi-factor authentication: Configure multi-factor authentication (MFA) for WiFi network management and key devices, requiring multiple verification steps when logging in to enhance access security. Even if the password is leaked, multi-factor authentication can prevent unauthorized access.
Security software configuration: Install and run trusted antivirus software and firewalls on all connected devices.
-
Regular backup and emergency plan: Regularly back up important data to ensure that key information can be restored after a security incident occurs. Develop and test emergency response plans to clarify the processing procedures and division of responsibilities in the event of an attack or leak, and ensure that it can be quickly and orderly restored and handled in actual events.

Only through the continuous improvement of information confidentiality technology, the continuous iteration of information confidentiality equipment, and the continuous enhancement of personal information confidentiality awareness, can we effectively respond to the threat of the rapid growth of the number of WIFI devices to the security of confidential information, and can we more safely obtain and transmit network information to improve social productivity and enjoy the convenience brought to us by network information.
If you are interested in TFN PHC12 wireless signal detector and other wireless signal/terminal detection and analysis equipment, please contact TFN sales team:
Email: info@tfngj.com
WhatsApp: +86-18765219251
Facebook: https://www.facebook.com/tfnfate